Applied behavioral research in information security
Research and Consulting in IT Security
Editor-In-Chief, Counter-Insider Threat Research and Practice (CITRAP)
I'm honored and very pleased to have been selected Editor-in-Chief of a new, peer-reviewed, journal devoted to disseminating empirical research and applied studies across the counter-insider threat research and operational communities. Because the insider threat is fundamentally a human phenomenon, our major aim in focusing the scope of the journal on social and behavioral sciences issues will help to position CITRAP as a thought-leader in the insider threat mission space.
Applying Insider Threat Ontology to Operational Insider Threat Programs
Currently, I am working with Cogility Software to provide subject-matter expertise and guidance in applying the Sociotechnical and Organizational Factors for Insider Threat (SOFIT) ontology to inform implementation of insider threat assessment models within Cogility's continuous intelligence analytic platform, Cogynt--which performs hierarchical processing of event patterns to support real-time risk assessment. This effort is being conducted to support the development of a robust insider threat program for a client within the U.S. Department of Defense. Cogility's scalable, behavioral analytic modeling approach aligns closely with my own research on interactions among and the dynamic nature of insider threat indicators.
In a previous consulting project, working with Noblis, I provided subject-matter expertise and consulting to support development of insider threat assessment models that are based on the Sociotechnical and Organizational Factors for Insider Threat (SOFIT) ontology. This project facilitated the application of SOFIT in a real-world operational environment in a U.S. Government organization within the Department of Treasury.
Insider Threat Research and Knowledge Engineering
This includes numerous projects on behavioral and technical indicators of malicious insider threats to information systems, spanning more than 15 years of research and development. Work with greatest impact has been the discussion of psychological/ behavioral indicators, ethical and privacy issues, and methods/metrics for evaluating effectiveness of detection systems and tools. Most recent research has focused on developing a comprehensive knowledge base of insider threat indicators that supports development of threat assessment models--the Sociotechnical and Organizational Factors for Insider Threat (SOFIT) ontology.
Unintentional Insider Threat
Conducted in collaboration with CMU/CERT, this research focused on identifying potential contributing factors associated with unintentional insider threats: individual(s) with a degree of trust and access to resources or assets within an organization, who (without malicious intent) carry out or facilitate actions that result in potential or actual harm to the organization.
Cyber Friendly Fire
This project, initiated by PNNL and conducted in collaboration with PsyberAnalytix, addressed cognitive factors,research needs, and training implications surrounding the problem of cyber friendly-fire – offensive or defensive cyber/electronic actions that unintentionally harm the mission effectiveness of friendly or neutral forces.
Cybersecurity Expertise and Workforce Development
PsyberAnalytix supported a CMU/CERT research project aiming to characterize cybersecurity expertise and to identify individuals with higher potential to excel in cybersecurity jobs. Results suggest that the most successful individuals possess not only domain-specific knowledge and skills but also certain psychological traits, and that organizational environments must facilitate expertise development.
Cybersecurity Risk Assessment
PsyberAnalytix supported this CMU/CERT research project aiming to improve the network risk assessment process by identifying cybersecurity factors that influence perception of network risk by information assurance and network security professionals. behavioral psychology it consulting information security
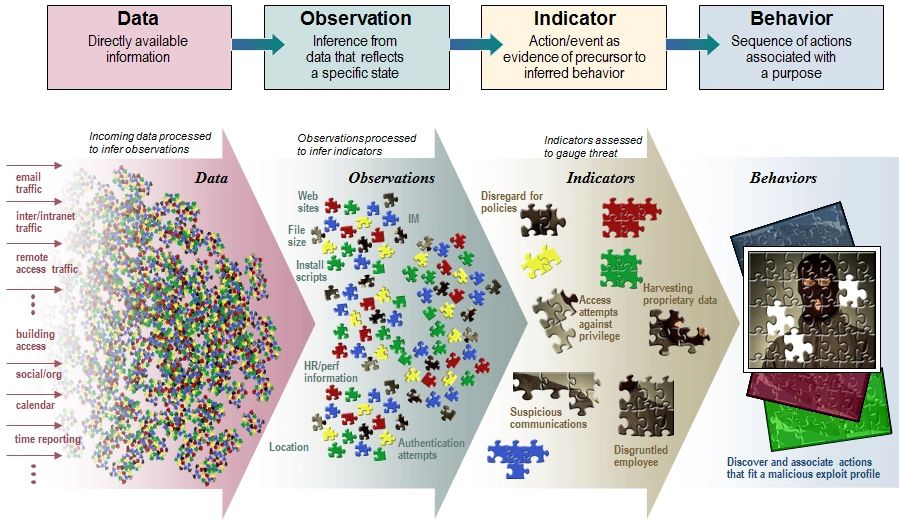
Conceptual Model
This "shredded puzzle" graphic, developed to describe the insider threat assessment process, has served as a conceptual model for, and has guided much of the information analysis and threat assessment research represented in the projects listed here.
Copyright © 2018 PsyberAnalytix LLC - All Rights Reserved.
Powered by GoDaddy